Reviewing the Top VPN Services: Our Methodology
Top10.com VPN reviews are based on objective facts. Our reviews are based on research via the VPN provider’s site, trusted 3rd party sites, customer reviews, and use of the product through free trials, or through paid use in some cases.
It is not always possible to use the product through its entire lifecycle. However, reviewers will try the signup process, make customer service queries to check response times and perform any other possible function within the review period.
For the rest of the information, we rely on what the brand says about its own product offering, customer reviews, and complaints, ratings from independent agencies like the BBB, and trusted journalistic publications.
Some of the key features we compared when looking at the VPN services on our list were:
- Price
- Number of servers
- Supported software
- Netflix access
- Logging policy
What You Need to Know Before Choosing a VPN
The best VPN is the one you notice the least. So choosing a VPN is a bit different than, say, buying a car. The factors that matter most--security, anonymity, reliability--are things you will only notice when they aren’t up to par.
Here are some key questions to ask yourself:
What will you use a VPN for? Are you planning on streaming Netflix? Downloading torrents? Avoiding intrusive government censors? Make sure the VPN you choose is able to accommodate your intended uses.
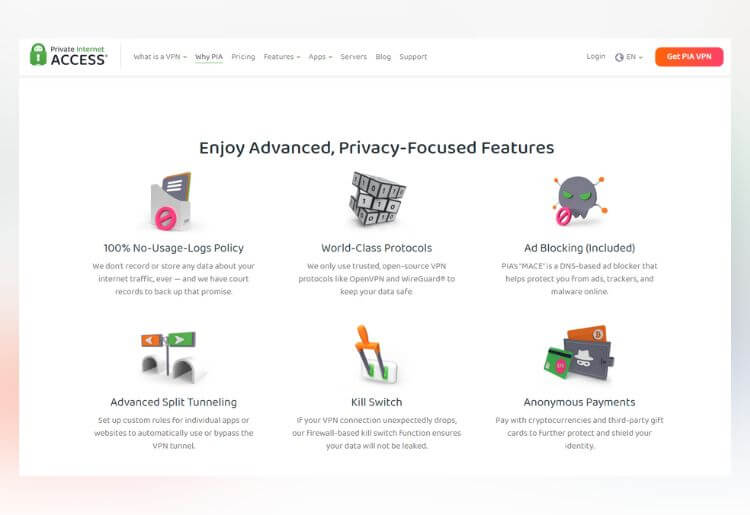
What level of privacy do you require? Different providers have different data encryption types and privacy standards. Some guarantee a no-logging policy, while others may share some of your data with third parties. Determine how important this is to you and find the service that best aligns with your needs.
How many people will be using it? VPN services can often be used by multiple people, though the number differs from one provider to the next. Whether you have a family, roommates, or will be the sole user, this can help you whittle down your options.
What Types of VPNs Are There?
Not all VPNs excel at the same things. The best VPN for Netflix, for example, may not necessarily be the best VPN for downloading bittorrents. Some VPNs specialize in streaming, while others may be better for overall anonymity, geo-spoofing, or Android users.
Are VPNs Safe and Secure?
Yes, though your security is only as strong as the VPN provider you choose. A reliable, well-reviewed VPN is trustworthy and more than capable of protecting you and keeping your internet activity private. There are questionable VPN providers out there, though, and they’re best avoided.
How can you know? Look for privacy and encryption standards. A good VPN service will have strong encryption protocols, clearly stated privacy policies (like no logging), and strong security features like DNS leak protection.
Tips on VPN Providers
There are numerous choices when it comes to VPN services. Narrow down those choices by focusing on the most important features.
Look for a service with fast speeds so your connection is smooth, strong security features so your connection is private, and easy functionality so that you can access and use your VPN without any hassles. Also, look for one that offers P2P file sharing, and make sure the price is right.
Here are a few more things to keep in mind:
Don’t settle for cheap. Listen, we all want to save money. Price is a reasonable measuring stick when shopping for any product or service. But you get what you pay for, and with VPNs in particular, a cheap service might cause you more harm than good. A poor VPN can give you an illusion of safety, causing you to be looser with your internet activity while actually leaving you vulnerable. We’re not saying you need to opt for the most expensive option. But don’t let price alone sway you. Privacy does have a cost, if it’s the difference between an unknown and a well-respected provider, it’s worth the few extra bucks to make sure you’re actually protected.
Customer service matters. Internet security is an important concern these days, and it’s up to each of us to be proactive in making sure our information is safe. A reliable and responsive customer support team is crucial for when you have concerns about your privacy or need to troubleshoot an issue. And besides, solid customer support is usually indicative of a trustworthy company. Live chat support, 24/7 availability, and stocked FAQs are all positive signs that the provider has your back.
How Much Does A VPN Cost?
The average price for a legitimate VPN falls around $4 per month. Some start as low as $2.50 and others may go as high as $9.99 per month or higher.
One thing to keep in mind is that the price fluctuates with the length of your subscription. The same company may charge $3 per month if you purchase a long-term subscription and $12 per month if you opt for a single month. Purchasing a VPN for 2 years, for example, can drastically reduce the price, while paying month to month can cause your monthly cost to skyrocket.
There are free VPNs available, though it’s advisable to avoid them or approach them with caution. While a free VPN may be sufficient for extremely rudimentary web tasks, it’s unlikely to have the tech and security measures necessary to protect activities like online banking, downloading, and streaming.
Other Brands We Reviewed
This list of 10 VPNs is composed of companies that chose to partner with Top10.com. In total, we reviewed over 50 brands when doing our research into VPN providers, with new brands being reviewed on a regular basis. Interested in learning about the prices and features of some big VPNs that don't appear on this list? Check out our in-depth reviews of some of these big names in VPN:
A VPN for Any Occasion
VPN services provide an invaluable service for anyone using the internet. While people will opt to use a VPN for different reasons, it will benefit the whole range of internet users, from casual users to Netflix fans, hard-core gamers, and of course those who do online banking and shopping. Whether you're looking for more privacy or security or you want to access geo-blocked content or download and share files, a VPN provides you with the advantages you are looking for.
ExpressVPN is currently the best VPN service on the market. It offers a huge network of servers, excellent speeds, and admirable privacy policies that ensure security and anonymity.
It depends on your VPN provider. If your VPN plan includes unlimited bandwidth, you can leave it on without fear of being charged more. If your plan doesn't include unlimited bandwidth then it's a good idea to turn your VPN off when you're not using it.
Traditionally, no. Legitimate VPN providers do not steal data. That being said, there are many free and lesser-known providers out there with unclear privacy policies, so it's always a good idea to research a companies policies and repuation before making your decision.





.20191122102008.png)








.20191122102008.png)